Some cool turned components china images:
Tibet. China.

Image by kc7fys
I was chatting on the web with Qingchen, a schoolteacher buddy of mine in China. I helped her set up a patch on Flickr that makes it possible for her to view otherwise censored content material. (Flickr, along with several other websites, are filtered in numerous parts of China).
We generally speak about existing events and culture. She asked, "Did you hear about the Olympic torch in France and elsewhere?" She also showed me a video of "hooligans" attacking a handicapped girl who was trying to carry the torch.
What was our usual great-natured tête à tête somehow turned bitter as I asserted the usual Western line that China is crushing Tibet’s culture–and she carried on with "CNN is all lies," "we are helping Tibet to modernize," "Tibetans are violent hooligans," and that the Dali Lama (sp?) is fomenting this "separatist" sentiment.
Politics aside, the argument ended badly, and left a sour taste in my mouth.
Cyberwarfare amongst the U.S. and China
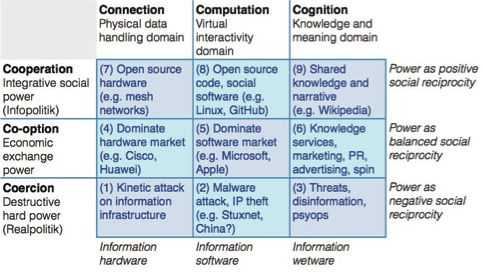
Image by jurvetson
At the Churchill Club leading ten tech trends debate I disagreed with the propositions that “Cyber Warfare Becomes a Excellent Thing” and that “US is the Supreme Cyber Security Force in the Planet and its Major Force citizens accept complete observation by the functions of a police state. A devastating electronic attack final results in govt. militarization of main gateways and backbones of the World wide web.” I have troubles with the “goodness” in the very first prediction, and although the U.S. could argue that it is the greatest, I don’t think the trend is toward a sole superpower in cyberspace.
The NSA TAO group that performs the cyber–espionage pulls 2 petabytes per hour from the Net. The networking infrastructure to support this is staggering. Considerably of it is distributed amongst the beige boxes scattered about in plain view, usually above ground on urban sidewalks. When President Obama receives his everyday intelligence briefing, more than 75% of the info comes from government cyberspies. (BusinessWeek)
Cyber-offense might be very various than cyber-defense. Some argue that open disclosure of defense modalities can make them stronger, like open supply software. But offensive tactics need to have to be kept private for them to be efficient more than as soon as. This leads to a lack of transparency, even inside the chain of command. This leaves open the possibility of rogue actors — or basically negative regional judgment — empowered with an capability to hide their activities and continual conditioning that they are “beyond the law” (routinely ignoring the laws of the nations where they operate). We might suspect that rogue hacking is already happening in China, but why ought to we expect that it wouldn’t naturally arise elsewhere as well?
Considering that our debate, the Washington Post exposé reported:
“Chinese hackers have compromised the styles of some of America’s most sensitive and sophisticated weapons systems—including important components of the nation’s missile defenses, fighter aircraft and warships… Also compromised had been designs for the F/A 18 fighter jet, V-22 Osprey, F-35 Joint Strike Fighter, UH-60 Black Hawk helicopters and the Navy’s new Littoral Combat Ship meant to prowl the coasts.”
And these days, a new report from the U.K. Defense Academy, entitled The Worldwide Cyber Game suggests that my mental model could be a bit antiquated.
Shall we play a game?
“When the Internet first appeared, the cultural bias of Western nations was to see it as a wonderful and welcome innovation. The fact that it designed security problems somewhat took them by surprise and they have been reluctant to respond.
In contrast, states such as Russia and China saw the Internet as a possible threat from the outset, and looked at the issue in the round from their viewpoint. They formulated strategy and began to move pre-emptively, which has allowed them to take the initiative and to some extent define the Cyber Game.
As a result, cyberspace is now justifiably seen by Western countries as a new and potentially critical avenue of international attack, which need to logically be militarized to protect the nation.
But what if details abundance is so deeply transformative that it is altering not only the old game among nations but the international gameboard itself? In this case, we require a distinct approach, one particular that seeks to completely appreciate the new game and gameboard ahead of making suggestions for national safety.
The ability of national governments to recognize and tame the Worldwide Cyber Game, just before it requires on an unwelcome life of its personal, may possibly be the vital test for the effectiveness and even legitimacy of the nation state in the data age.” (p.107)
The China Hypothesis
“It tends to make comprehensive state-bankrolled purchases of numerous critical parts of the neighborhood economies and infrastructure under the guise of independent commercial acquisitions. These incorporate contracts for provision of national World wide web backbones, and equity stakes in utility businesses. These allow it to control ever bigger components of the target economies, to install national-scale wiretaps in domestic networks and, in impact, to spot remote off-switches in components of critical national infrastructure.
Finally, to round off the effort, the ‘competitor’ simultaneously tends to make a massive work to build its personal domestic understanding sector, sending students around the planet in vast numbers to find out local languages and obtain sophisticated technical capabilities. In some cases, these students even manage to receive funding from the target nation educational systems. This work, which only pays off on long timescales, permits it to consolidate and make complete use of the information it has exfiltrated from around the globe.
If it is allowed to continue for lengthy adequate, the target countries will find that they have lost so significantly autonomy to the ‘competitor’ country that they are unable to resist a complete cultural and financial take-over, which is eventually accomplished without open hostilities ever becoming declared, or at least not of a type that would be recognizable as industrial-era conflict.
National geopolitical technique can be disguised as normal commercial activity and, even if this is noticed, it can not be challenged within the legal systems of target countries. Hence an international-scale offensive could be mounted with out it ever becoming understood as such.
These issues are somewhat reminiscent of the industrial cartelization technique pursued by Germany in the years operating up to the Second World War. This meticulously orchestrated type of financial warfare was properly invisible since it was positioned in the cognitive blind spot of British Empire industrialists. Until war broke out, and the deliberately engineered shortage of materials became apparent, they were unable to see it as anything but apparently profit-searching for industrial technique on the part of German business.
What sort of response ought to be made to a strategy like this… is retaliation of any type acceptable? Need to the Cyber Game be played as a zero-sum game? The important issue is that the technique requires IP theft on a grand, certainly international scale. This is actual destruction of worth for these organizations and agencies who have been targeted
Is there any other way of searching at this? Possibly the a single thought that trumps Western outrage at the notion of details theft is to recall that it can be stolen with no being lost, although it might be devalued. It may not be the understanding itself but how we generate it and use it that is essential. In this view, the Cyber Game, becoming in the end expertise-based, is genuinely a non-zero game. Amongst financial players of the Cyber Game, this understanding is progressively turning into an approach that author Don Tapscott calls ‘radical openness’.
A accurate understanding-era method could not be stealing info but sharing it, playing the Cyber Game higher on the gameboard, as World wide web pioneers have been undertaking all along. Perhaps Western democracies ought to respond to China’s alleged actions in the identical way. Dare they choose to reframe in this way?” (pp.52-eight.)
The Future
“The most probably type of conflict is now civil war in countries with governments referred to as anocracies, neither fully democratic nor totally autocratic.
Earnings polarization is rising inside wealthy nations, as a side effect of globalization, and is hollowing out the middle class. Commentators and researchers have noted this effect especially in the US. Whether this increasing polarization could raise the danger of civil war in wealthy countries is questionable, as extended as their governments remain powerful. This itself will be a function of how nicely they adapt to the evolving details atmosphere. If they fail, and a combination of economic, financial and environmental crises threaten the potential of governments to maintain the top quality of life, then internal conflict is entirely attainable.” (p.74)
And as I try to look farther to the future, the offensive cyber-code and autonomous agents of right now are not so distinct from the bio and then nano-weapons of tomorrow. The cell is but a vessel for the transmission of code.
I feel humanity will cut its teeth on cultural norms and responses (police state, cyber-counter-guerillas (beyond governments to posses and bounty hunters), and a societal immune technique for the crazy ones) in response to the imminent cyber threats… and then we will face bio threats… and lastly nano threats. So there is little reason to concentrate on the latter until we have solved the former.
here are some berries I made for skynet to make it feel greater for beginning globe war iii

Image by harold.lloyd
So SKYNET got all mad simply because it got hacked from China and now China will get all mad back and people will point and say angry factors and frown and ultimately the computer systems will take more than and bomb us all to bits till John Connor takes over and SKYNET is destroyed. Until then? Please take pleasure in the berries.
Boom! go the berries. Boom!
